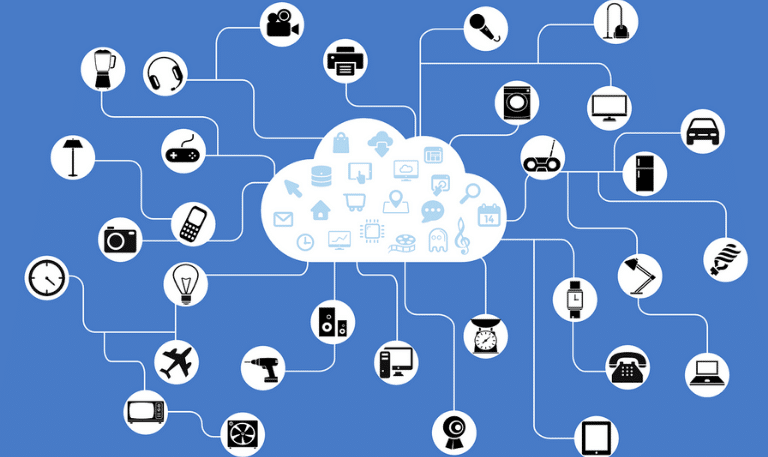
Much of the growth in IoT is being driven by the availability of network-capable microcontrollers powering everything from toys to heavy industrial equipment.
Yet, as our things become increasingly connected, bad actors are uncovering more and more potential vulnerabilities. Traditional IT security is often ineffective when it comes to IoT devices because of their multiple communication channels and connectivity types, the number of backdoors and access points increase exponentially.
‘Internet of Threats’
This led the founder of the Kaspersky anti-virus company, Eugene Kaspersky, to once remark that IoT could be said to stand for the “Internet of Threats”.
IoT, along with cloud and other tech developments, has blurred the edges of the traditional network perimeter, making firewalls more porous and easily penetrated. As a result of the growing challenges, IoT security has become a specialised and rapidly growing market that is predicted to grow at over 30 per cent a year from USD 8.2 billion in 2018 to USD 35.2 billion by 2023.
A recent Microsoft report on IoT security warns that with new security threats constantly surfacing, organisations need to shift to a more holistic, proactive approach that factors prediction, prevention, detection and response into every layer of the IoT ecosystem, no matter where devices live.
5 Key Risks
The report identifies 5 key risks posed by compromised IoT devices:
-
Data pollution—Instead of stealing data, compromised IoT devices could be used to insert or alter data. For example in smart metering systems based on input from remote sensors, billing data could be compromised.
-
Bricking—Some attacks on IoT devices are designed to shut devices down permanently, a process known as permanent denial of service (PDoS) or “bricking”. PDoS attacks continue to grow in frequency, and may increasingly be linked to ransom demands in future.
-
Data breaches—For example, hackers have often targeted office printers because their security is pretty scant. Once in, they may be able to access print jobs, network passwords etc. In terms of Australia’s Notifiable Data Breaches scheme, a compromise of personal data by a company could result in penalties of up to $2.1 million, which is a real blow to the bottom line of a business.
-
Using hacked devices for malicious activity—Because hackers can comprise equipment and run rogue, or access private data, companies are under constant threat of a bad news day—which can be a PR nightmare (not to mention the collateral damage).
-
Network access—Unsecured IoT devices can be used as back doors to corporate networks quite easily. The aforementioned Microsoft report cites the example of an internet-connected fish tank thermometer that was used to compromise a casino’s network (not the kind of royal flush you’re after).
To help combat this California has ruled that from January 2020, any manufacturer of a device that connects “directly or indirectly” to the internet must equip it with “reasonable” security features—including a unique password for each device, or must force users to set their own password the first time they connect.
However many of the billions of IoT devices in use today were shipped with default usernames and passwords. This has led to several attacks on IoT devices exploiting this vulnerability, including the Silex attack of June 2019, which “bricked” several thousand IoT devices.
Anything but smart
It is ironic that IoT-connected things are often referred to as “smart devices”, because in many ways the challenge is that from a processing power and security perspective they are anything but smart.
As a result, many experts warn that the best solution to IoT security is to make networks smarter. This includes implementing systems to collect and analyse multiple different types of network security event information, and combining multiple layers of defences both at the edge and within the network.
No perfect protection
Every IoT sensor is not just a potential entry point for intruders but also a source of valuable data or a connection to equipment, customers or suppliers. In an increasingly digital, online and interconnected world, isolation is simply not a realistic solution, and perfect protection is unattainable. A more effective goal is to be as adaptable and resilient as possible.
Your security needs can be brought into focus at Security 2019, held at the ICC Sydney from July 24-26. Register free now to attend.