Tech Trends
Safety Makes Us Better At Everything We Do
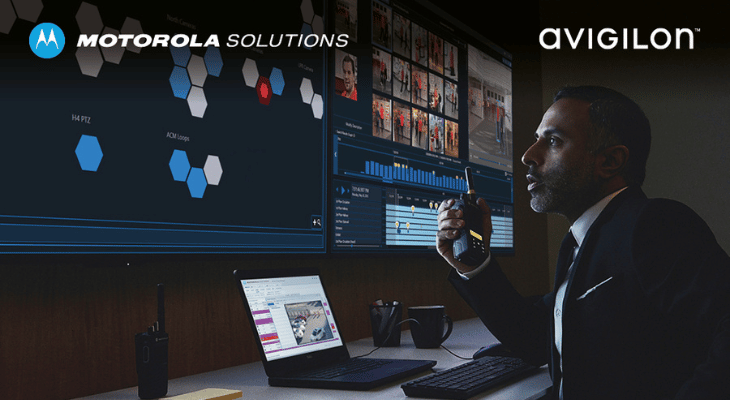
At Motorola Solutions, they’re building the foundation to drive a safer world. They have combined 90+ years of mission-critical technology experience, leveraged the expertise of acquired companies and strategically directed our R&D to build the first unified and connected technology ecosystem that integrates critical communications, video security, data and analytics on a common operating platform. […]
Focus on Biometrics
The launch of the iPhone back in 2008 was a watershed moment in the history of biometrics. Up to that point, biometrics such as fingerprint and facial recognition had been somewhat unreliable, slow, and plagued by false acceptance and rejection rates. Furthermore, a significant proportion of the community felt there was an uncomfortably high probability […]
Focus on Cyber Security
Over the last decade, the evolution from standalone analogue security systems to IP networked systems has given rise to an increasing focus on cyber security. As we move towards a true Internet of Things (IoT), every system, device and piece of hardware or software represents a potential point of vulnerability. Meet Jo, an expert with […]
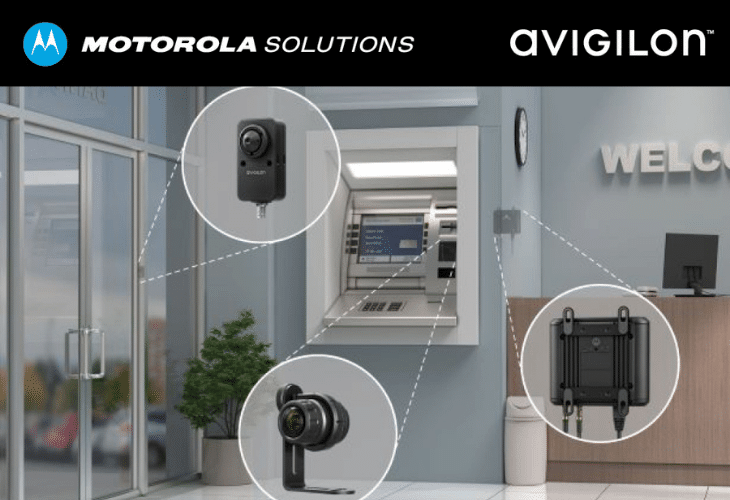
Meet the Smallest Avigilon Camera for the Most Challenging Spaces
The Avigilon H5A Modular camera is designed for areas with limited space or require a discreet and unobtrusive monitoring solution, such as ATMs, police interview rooms, retail checkout counters, building entrances or casino gaming tables. The camera’s flexible imager modules can easily be positioned in different orientations to help capture the most optimal view of […]
5 ways AI can help strengthen security in a post-pandemic world
The role of machine learning and AI in a post-pandemic world across key sectors, like retail, and building and construction is continuously increasing.
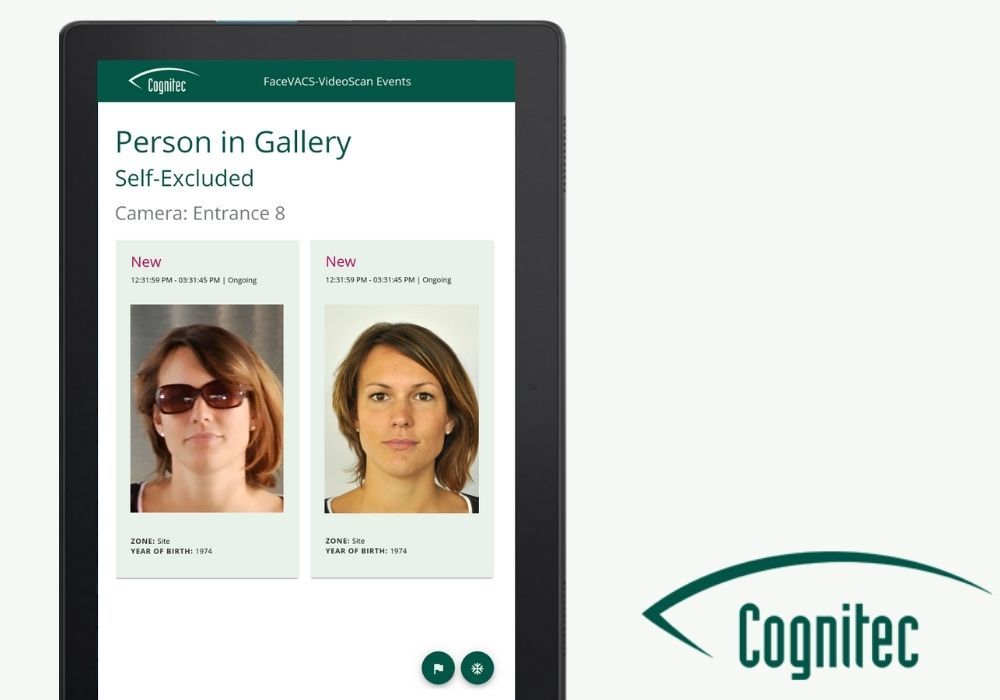
Contactless, Quick, Dependable: The Power of Face Recognition
Then came a virus…and now the world is looking for new methods to stay safe, healthy and protect against viral infections. How can we continue to authenticate people without touching devices, reopen travel with contactless processes, or detect people not wearing a mask in crowded spaces?
5 Smart Security Solutions in the Fight Against COVID-19
As restrictions ease at varying rates across the country, workplaces that are re-opening have an increased responsibility to ensure that the health and safety of staff and customers remains a top priority in the ongoing fight against COVID-19.
How Do We Solve the Biometrics Security Puzzle?
Refining biometric technologies is critical to a future where every point of physical contact is considered a possible health risk.
Thermal Technology: Ensuring Effectiveness
As states and territories across the country ease restrictions, we continue to see varied initiatives for mitigating risk. Thermal cameras are becoming a prevalent measure for non-contact temperature screening in public spaces and workplaces – a factor helping to fuel the growth of the thermal camera market, now tipped to increase by a CAGR of 7.29% to reach USD 6.41 Billion by 2025.
AV Courts New Business in Lockdown
Advances in technology have freed individuals from the restraints of time and distance. But what about those who have been restrained by the law? The deployment of technology in a correctional facilities and courtrooms is a complex issue, and mistakes can have serious consequences Paul Skelton reports.